Something big happened last week — Gartner® issued a report* that definitively establishes API security as its own essential category in securing platform services. It’s not a subset of the WAF, it’s not an add-on to an API gateway — it’s its own category.
With any new technology, people love to ask, “is this a product or a feature?” The security industry spurs this debate more than any other tech sector, with a constant cycle of startups and acquisitions. For the API security market, we believe Gartner just ended that debate.
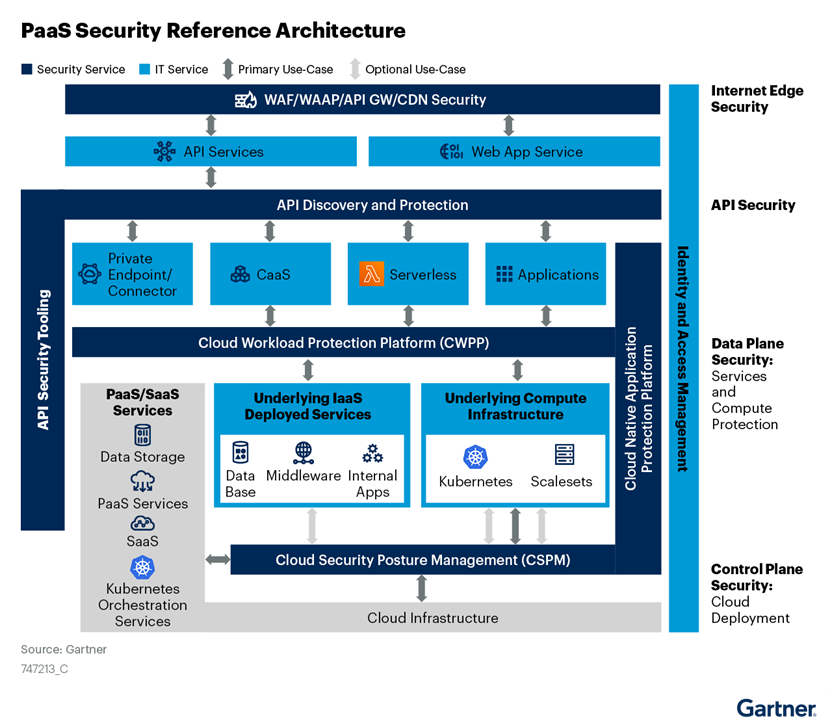
The report, focused on guiding organizations on how to improve PaaS security, includes a Security Reference Architecture showing what’s needed to protect these platforms. The following version of the architecture is modified to better illuminate its key pillars — you’ll find the original at the bottom of the blog.
Correcting an inaccurate and incomplete perspective
For years, Gartner built this security reference architecture on three pillars:
- WAF, WAAP (web application and API protection), API gateway, and CDN — which Gartner describes as protecting the edge
- CWPP (cloud workload protection platform) — securing the data plane
- CSPM (cloud security posture management) — securing the control plane
All this time, Gartner has graphically nested API security within the WAF/WAAP/gateway/CDN pillar. Gartner coined the term “WAAP” to convey that WAF and API protection capabilities would be blended.
Does it really matter how Gartner draws a picture? Yes — it really does.
In multiple research notes, Gartner has acknowledged in the writing of the reports that many organizations need dedicated API security, but we all know the power of a picture vs. words, and API security was not “in the picture” … until now.
API Security Takes its Rightful Place in the Picture
API attacks have tripled in the past six months. This Gartner pictorial change — this visual clarity that API security is “its own thing” — will do more than 1000s of words ever could to educate organizations that their WAFs and gateways simply don’t cut it for API security.
With this new architecture, Gartner affirms that existing tooling leaves gaps in API security. Until now, every security architect, AppSec lead, and head of API platforms who has had to make the case for investing in API security has always needed to fight the “but we already have a WAF so we’re covered” battle.
This visual representation empowers those leaders with Gartner-based evidence of the transformed API security landscape, giving them the ammo they need to explain that:
- API attacks are not the same as application attacks
- APIs are an enormous hacker target and need dedicated protection
- WAFs and gateways can catch only pre-defined, known attacks
- APIs, and therefore API attacks, are unique to each organization, so finding and stopping these attacks requires context with a deep understanding of API behaviors
This Gartner security reference architecture validates what those leaders have been saying all along — that a few cursory features stapled onto a WAF or gateway do not equate to API gateway security. The tooling is different, the architecture must be different, and making the right security investment is crucial.
Everyone knows the power of having Gartner place a technology on a reference architecture diagram — it establishes the product category, and it signals a robust and meaningful market. I’d love to say this architectural shift signals that Salt Security has finally arrived. But the reality is, Salt has been in the lead here for years.
Salt pioneered this market more than five years ago. The Salt vision has always been to accelerate business innovation by making APIs attack proof. We’ve been in the lead from the start — with the most customers, the most proven platform, the most advanced algorithms, and the broadest application ecosystem support. With this report, Gartner is now amplifying the reality that organizations must take a new approach to protecting APIs.
And we couldn’t be happier. To learn more about how Salt can help defend your organization from API risks, you can connect with a rep or schedule a personalized demo.
* Gartner report: Advance Your Platform-as-a-Service Security, 25 August 2021, by Richard Bartley available to Gartner clients of GTP (Gartner for Technical Professionals) at https://www.gartner.com/document/4005128