“Shift Left" approach for proactive API security
APIs are more than just code. They combine business logic, configuration, and data that create risks that should be mitigated as early as possible in the SDLC.
Salt's “Shift Left" approach for API security stops the endless chase for vulnerabilities by allowing you to create an API security policy and enforce it from design to cloud.
SecDevOps for APIs done right
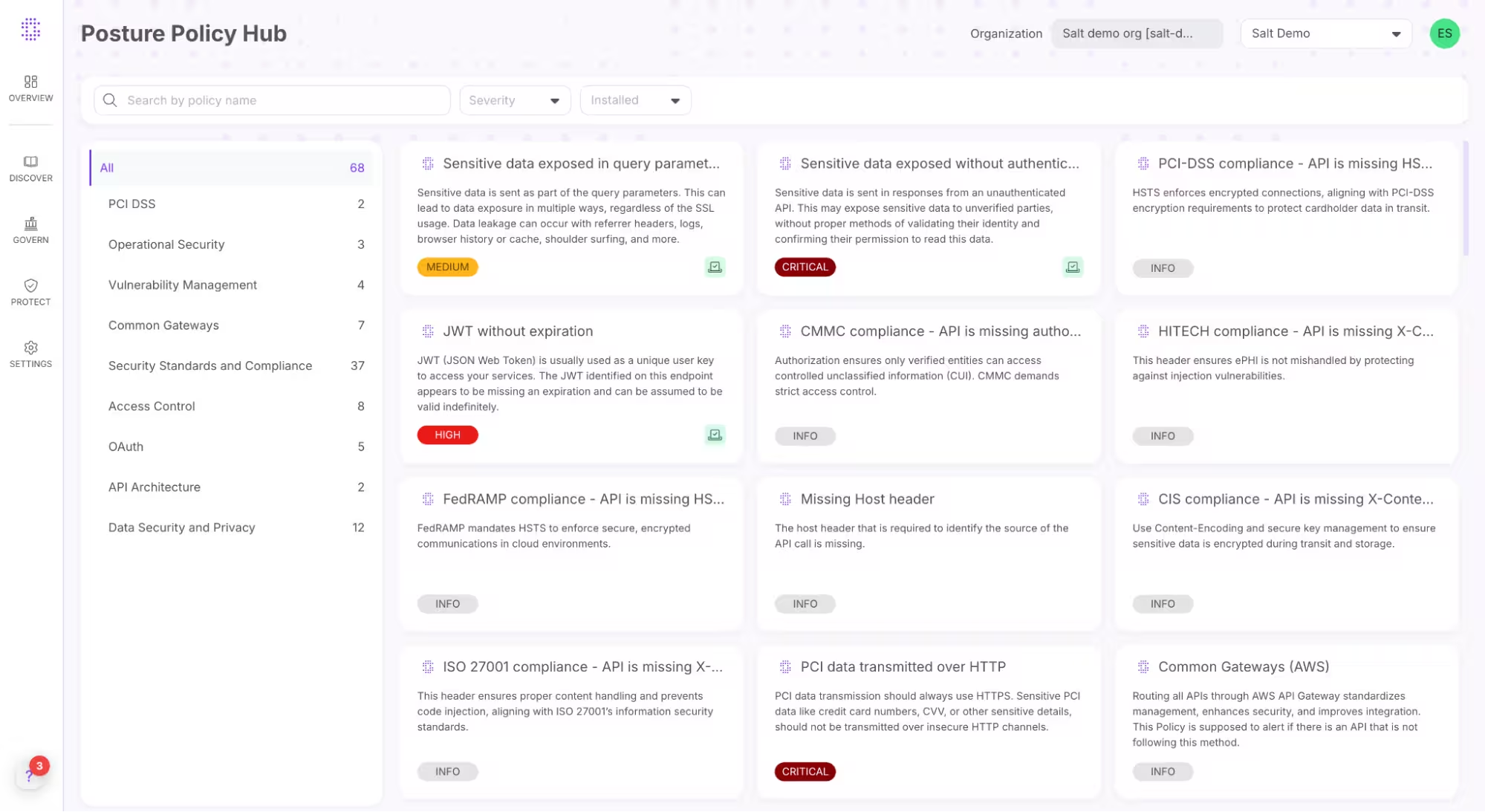
Only Salt provides a comprehensive and customizable library of out-of-the-box API security and technical standards that span security and compliance risks, such as PCI from the API design phase through the build process and into production.
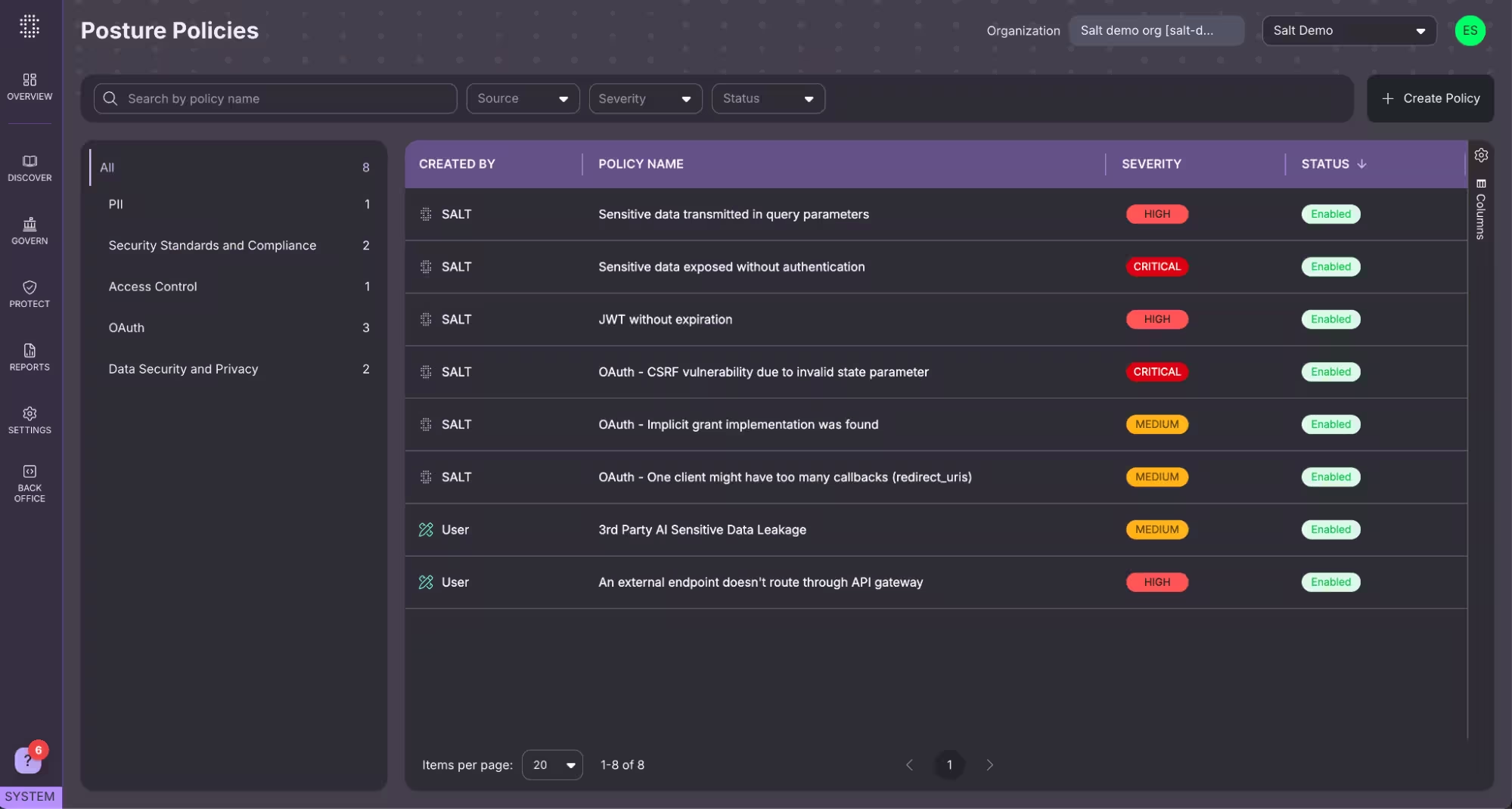
Learn more01 Building API security posture standards
Salt gives you best practices and other standards making it easy for everyone to be focused in the same direction.
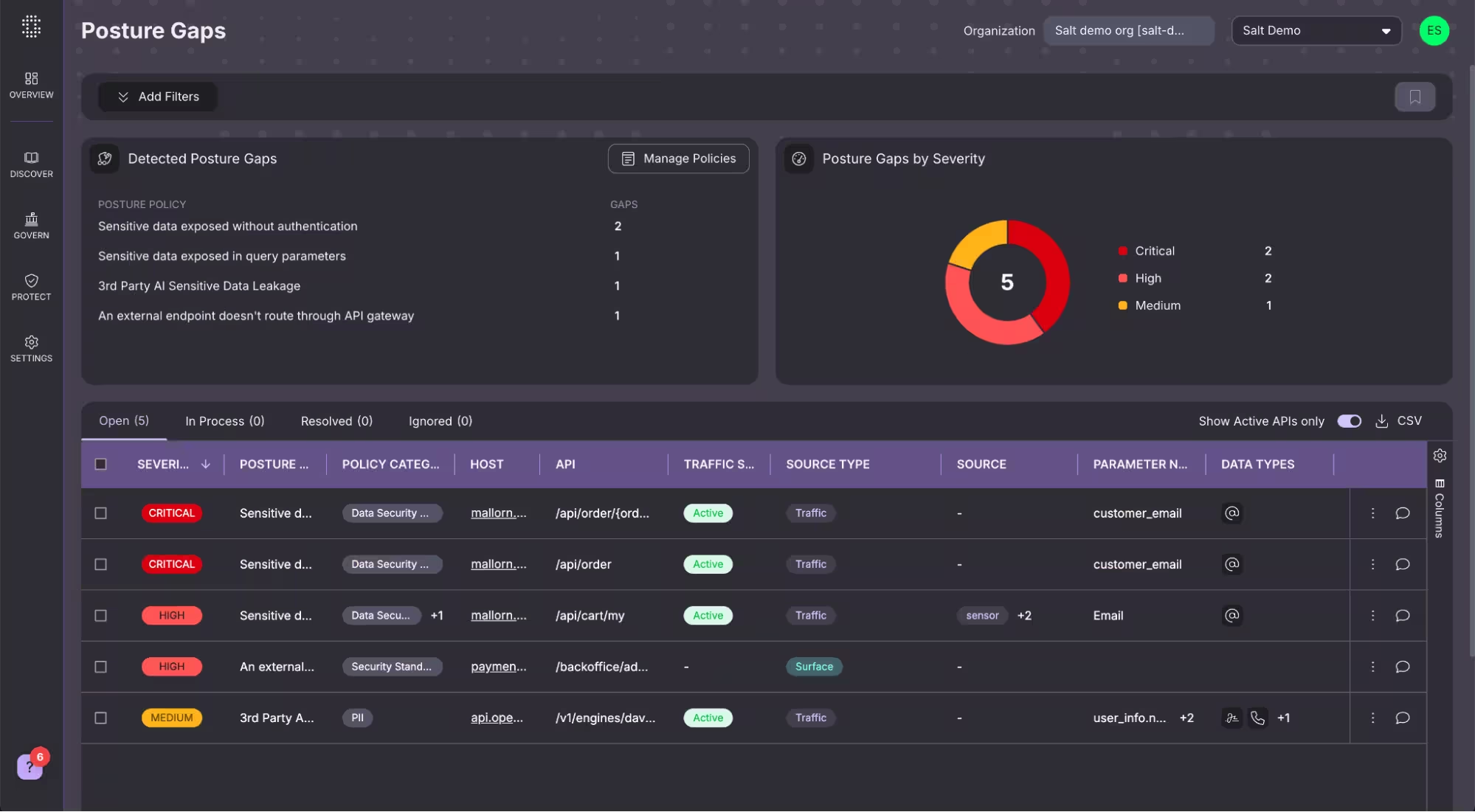
- Best practices. Salt provides API security governance by providing a comprehensive set of best-practice security policies and configurations, as well as inspecting and assessing APIs for compliance with those policies through the SDLCs.
- Compliance to policy. Salt also identifies sensitive data sent over first — or third-party API requests or responses and assesses compliance with data security policies.
02 Designing APIs with security in mind
Provide early assessment and developer training to ensure you are identifying issues early.
- Early assessment. Assess security posture compliance at design time with immediate feedback for developers.
- Enhanced developer education. Increase developer education, enabling them to continuously improve the security of the APIs they build in the future.
- Know standards. Standards Education, GenAI LLM training and OAS/API Contract Validation.
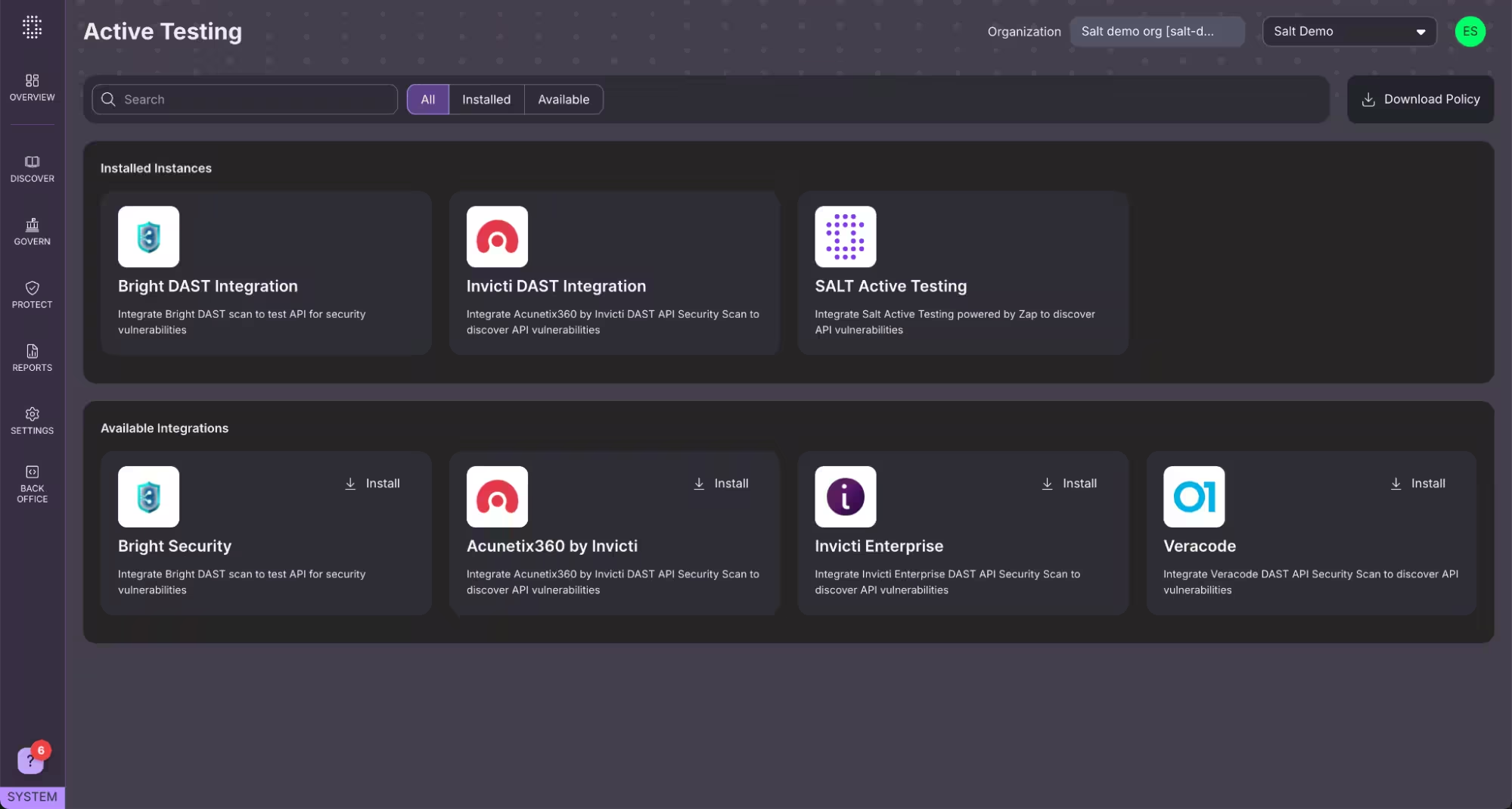
03 Enrich your AST program with API intelligence
Do the best testing possible with advanced insights and integrations.
- Accurate Ttesting. Salt automatically generates up-to-date specs for APIs and feeds them into your application security testing tool, allowing for accurate and API-specific testing with your existing tools (SAST/ DAST /IasT).
- Jira and Slack integrations. Send Jira tickets, Slack notifications, and other developer communications directly from the Salt platform with a loopback feed into SALT to ensure visibility to remediation status.
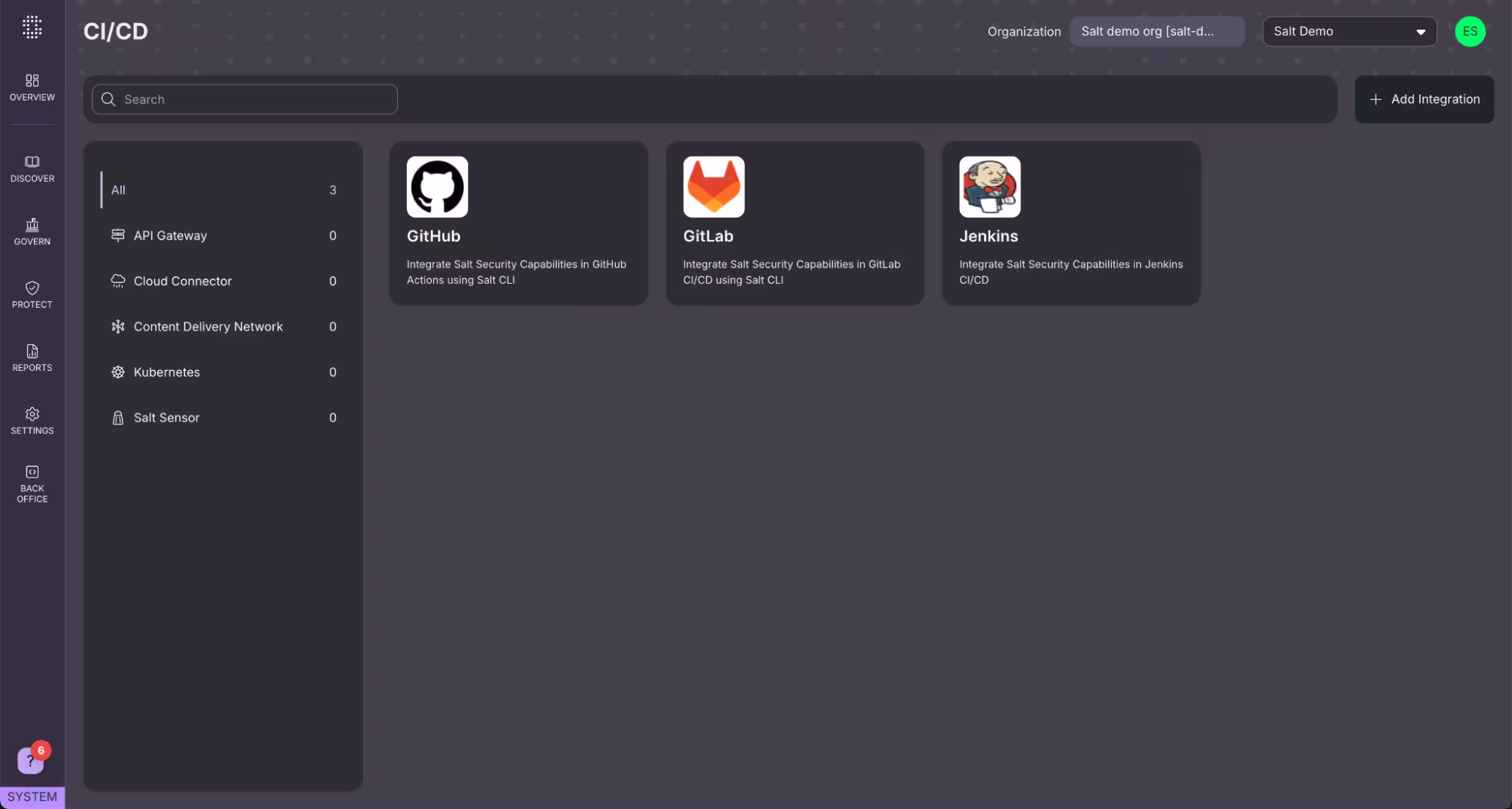
04 Quality gates
Salt continuously assesses security posture compliance in your CI/CD pipelines and staging, ensuring that security risks are not introduced into production.
- Conditional build approval. For APIs that Salt identifies as falling short of your security standards, you choose to allow that build to succeed but require the developer sign off on the risk.
- Comprehensive issue resolution. A Salt-issued ticket includes the details your dev teams need so they can address the security gaps and risks before releasing the build.
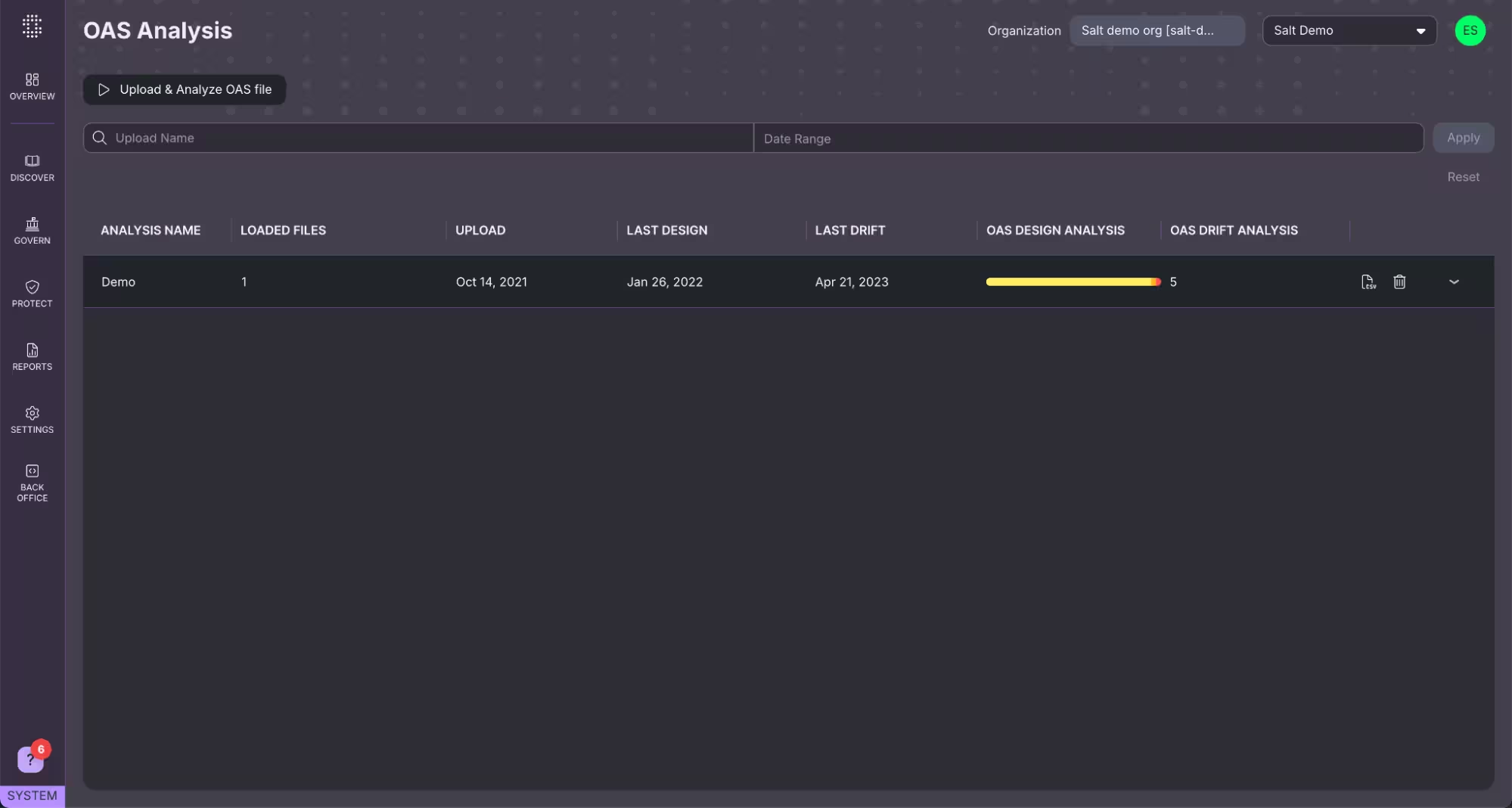
05 API drift analysis
Understand where you are drifting from the desired state.
- Documentation discrepancy analysis. Compare the findings to your OAS/Swagger files and see where your documentation and live API traffic diverge.
- Noncompliant data and behavior in run-time. Monitor how API’s are used and abused in production to ensure no drift occurs from previous posture.
What our customers are saying
“Salt has been a game-changer for our API security. We now have the visibility and control to protect our data, stay compliant, and build trust with our customers.”
—Peter Rios, Infrastructure and Information Security Manager, CISM, Kingston
Want to see the Salt platform in action?
Learn how Salt Security's leading API security platform can provide complete Posture Governance and API Behavioral Threat Protection.